Security is not only securing intangible assets. Security should include physical security. This is one way security was implemented a long, long...
Latest from the blog
How I passed my CISSP Note. By no means am I implying this is the only way to study the CBK or prepare yourself to pass the CISSP exam. It does not...
When we procure a system or software, we often leave the default settings as setup by the vendor. That might not always be good for security. One of...
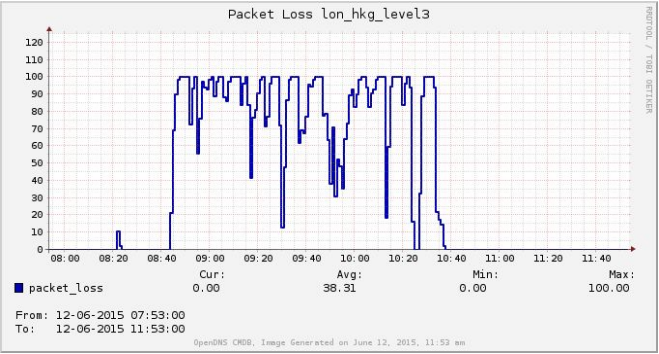
The Internet literally stands for interconnected networks. Essentially it is made out of individual networks. These individual networks are referred...
Wikipedia, the free encyclopedia turned on https as well as HTTP-STS or Http Strict Transport Security. This was announced on their blog. This comes...
One of the unfortunate side effect of the explosion of the information systems in recent times is the ever decreasing privacy of the individual...