It has been another busy GITEX technology week in Dubai. The myriads of security products were dominated by Machine Learning and Deep Learning in...
Latest from the blog
A popular software developed by a subsidiary of Avast were infiltrated. An unknown entity maliciously hid malware in the form of backdoor in Piriform...
The Wikipage of Equifax Inc. states. “Equifax is a consumer credit reporting agency. Equifax collects and aggregates information on over 800...
Driving back home, I asked myself, where will ransomware attacks takes us next? I then read this article on Ars Technica. It is chilling but not...
Another go for encrypted file sharing. This time it is from Mozilla better known for Firefox, the open source browser. The service named Send thought...
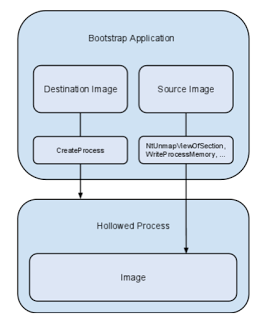
This is a good piece on process hollowing and atom bombing. If you ignore the marketing part of course.