In this week’s episode we will continue with Part 2 on Demystifying Digital Certificates.To take the most out of this week’s episode – If you have not listen to Part 1, I suggest you listen to the first before you listen to this...
In this episode, I want to shine a brigt light on an important yet frequently misunderstood part of online security: digital certificates. Certificates are essential in today’s digital world for safeguarding communication and confirming...
A great piece on what it will take to improve the safety of the connected world. Read it here.
Extended detection and response (XDR) captures threat data from previously isolated security tools throughout the organizations tech stack to enable easier, faster triage and efficacy in investigation, threat hunting, and accurately responding to...
Organizations are increasingly considering response capabilities within NDR solutions for dealing with threats detected through network traffic analytics tools, which are mostly focused on only detecting threats, and are largely focused around the...
A new malware kit to compromise ISC (Industrial Control Systems) is detailed in this whitepaper by Dragos.
Towards the end of November, a researcher from Alibaba discovered a fault (CVE-2021-44228) in a well known open-source logging library called Log4j. The researcher responsibly disclosed his finding to Log4j’s Apache Software Foundation...
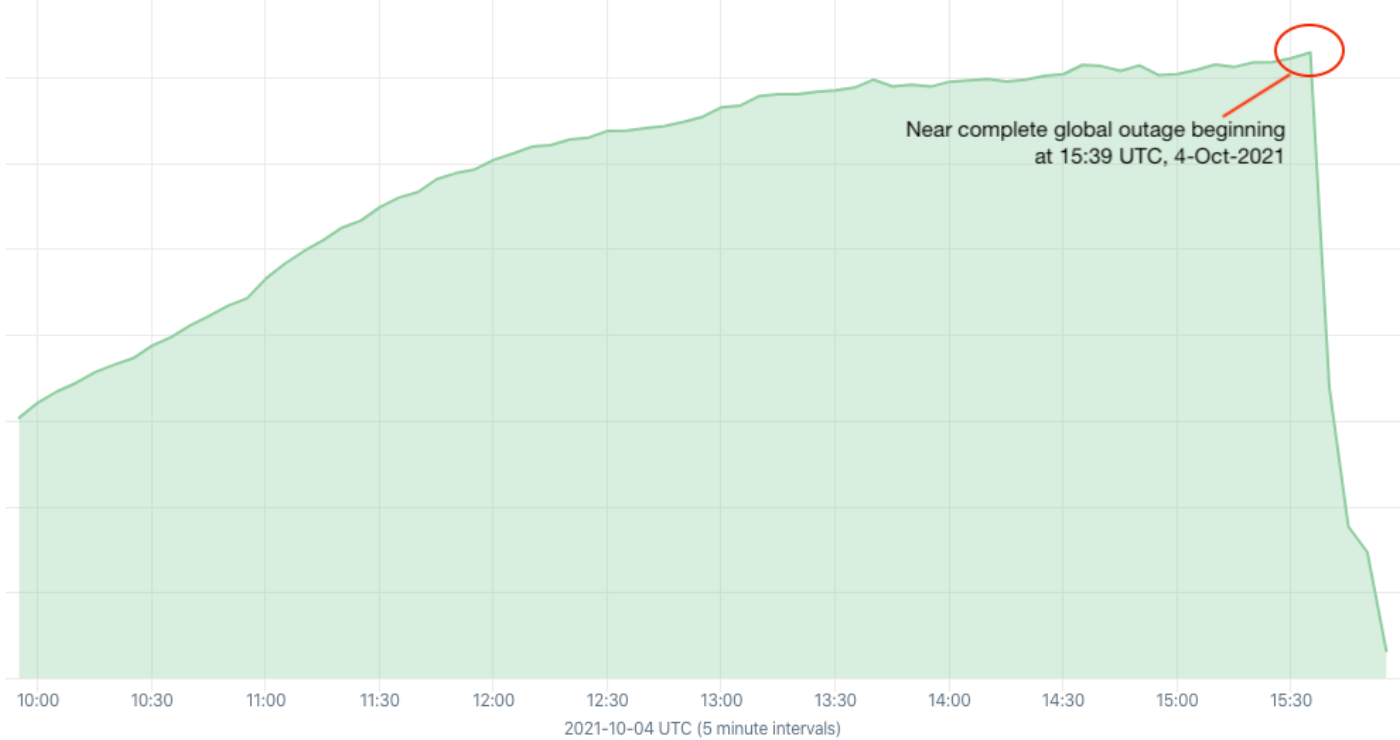
This is a developing story and the why is still a mystery. We starting to know the how.
CISA and NSA have released best practices documents on how to harden your virtual private network.
Apple has released a patch for ‘zero-click vulnerability. What is a ‘zero-click’? It is a flaw which lets hackers access devices through the iMessage service even if users do not click on a link or file. One can imagine the power...