In today’s episode, we cover two important data models and their applicability to security. I am talking about data lake and data warehouse. I will look into their similarity, differences and practical considerations surrounding these two...
This is episode 2 of on how how exactly cybercriminals join forces for profit. Make sure you caught up with episode 1 first before you listen to this episode.Lets continue demystifying their collaborative nature.But before that, we will recap...
It is true, there is no loyalty between criminals but there is a profit to be made between them.How exactly cybercriminals join forces for profit? We will answer that question in this week’s episode as we uncover the secret collaborations of...
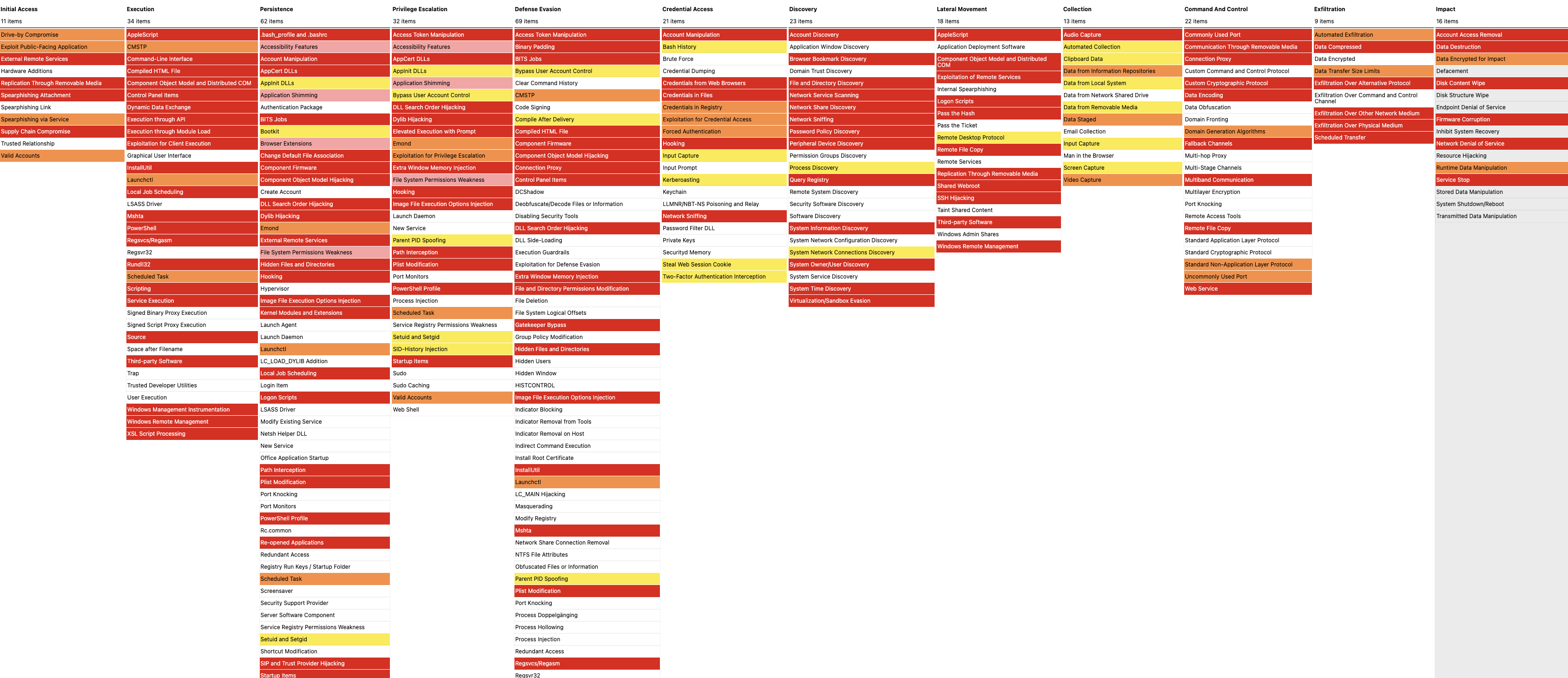
The ATT&CK Navigator is a web-based tool created and maintained by the Mitre organisation. The tools is used for annotating and exploring ATT&CK matrices. It is often used to visualize defensive coverage, red/blue team planning, the...
In this week’s episode we will continue with Part 2 on Demystifying Digital Certificates.To take the most out of this week’s episode – If you have not listen to Part 1, I suggest you listen to the first before you listen to this...
In this episode, I want to shine a brigt light on an important yet frequently misunderstood part of online security: digital certificates. Certificates are essential in today’s digital world for safeguarding communication and confirming...