Just before the turn of the year, Travelex, the foreign currency exchange service suspended their online services and took their systems offline after “a software virus was discovered”. They put out the following notice which is still...
The US-CERT has pushed out an advisory yesterday to warn customers of a potential cyber attack following the heightened geopolitics. You will need to review the potential attack framework and the accompanying recommendations listed further down the...
An application used by enterprises are utilized to deliver malware. Not any malware though, yes you guess it, ransomware! It is likely the same ransomware reported by Cisco Talos in April 2019. It is called REvil also known as “Sodinokibi...
A must read article to get your head around this. As the article puts it, this stuff isn’t vaporware dreams—it’s real, it’s here already, and it’s changing your life whether you realize it or not.
Ransomware attacks are often seen as just nuisance when you have a good backup. However it is a disaster for many businesses when you have no fallback. Remember a ransomware is a monster with two heads. One, it denies you access your data. Two, what...
Yes there has been yet another huge data breach. This time it is Capital One which according to Wikipedia “is a bank holding company specializing in credit cards, auto loans, banking and savings accounts headquartered in McLean, Virginia...
Security is a jigsaw. It has a lot of pieces (network security, email security, endpoint security etc) but to have the perfect fit, you have to align them correctly. You cannot replace a piece with a different piece even if you have more than one...
The Japanese government has passed a new law which will allow them to access IoT devices in JApan with default username and password. In effect the National Institute of Information and Communications Technology (NICT) employee will attempt to login...
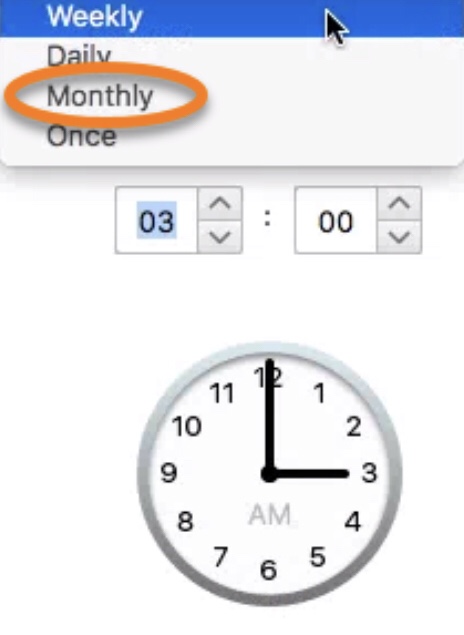
Lets look into the basics of schedule scan also known as on-demand scan (this includes right-click scan). In the days when endpoint relied on anti-virus alone, schedule scan played a critical role in complementing the real-time scan also known as on...
The general public are waking up to the reality that password alone is not a long term solution. More and more people are opting in for a more secure way to safeguard their digital life by way of enabling two factor authentication (2FA) -also known...