An application used by enterprises are utilized to deliver malware. Not any malware though, yes you guess it, ransomware! It is likely the same ransomware reported by Cisco Talos in April 2019. It is called REvil also known as “Sodinokibi.” Sodinokibi attempts to encrypt data in a user’s directory and delete shadow copy backups to make data recovery more difficult.
On unpatched systems, the flaw “allows people without valid usernames and passwords to remotely connect to the corporate network the device is supposed to protect, turn off multi-factor authentication controls, remotely view logs and cached passwords in plain text (including Active Directory account passwords),” Beaumont explains.
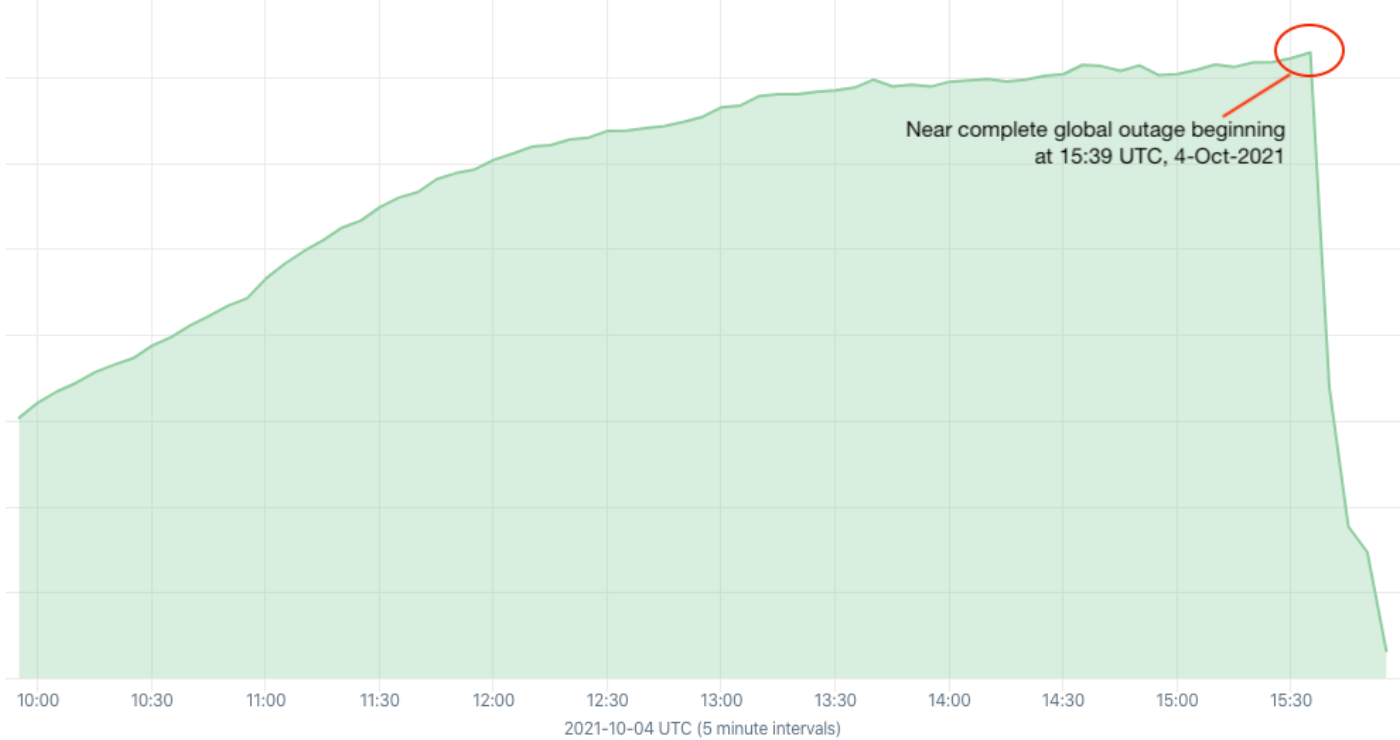
Lets go back to last year. Pulse Secure VPN, an enterprise remote access product was used to infect customers with ransomware. In October US CISA, US National Security Agency, and the UK’s National Cyber Security Centre sent out warnings to organisations about the danger of leaving their systems unpatched.
The Pulse Secure VPN was patched against what was described an “an incredibly bad” vulnerability (CVE-2019-11510)
As we know, organisations have a lot on their plate lately and although patching your systems should be a priority, not a lot of them come around to push those out soon enough.
It is critical companies patch often, patch early.