Listen to this very insightful episode on differentiating two important cybersecurity domains that are both intriguing and essential: Threat Hunting and Incident Response.We all agree that staying one step ahead of cybercrooks is paramount. But what...
This is another exciting episode of our cybersecurity podcast! Today, we’ve got a topic that’s is of great interest to all —the updated Payment Card Industry Data Security Standard version 4, or PCI DSS v4. If you’re in the world...
Today, we continue with part 2 the critical aspect of cybersecurity: incident response best practices. Given the unforgiving threat landscape, organizations face an ever-increasing number of cyber threats. Whether it’s a data breach, a malware...
Today, we delve into a critical aspect of cybersecurity: incident response best practices. Given the unforgiving threat landscape, organizations face an ever-increasing number of cyber threats. Whether it’s a data breach, a malware attack, or...
Cybercriminals are constantly adapting their tactics, making it crucial for organizations and individuals to stay one step ahead. That’s where cyber threat intelligence comes in.Whether you’re a cybersecurity professional looking to...
In a world where data breaches have become all too common, understanding the intricacies and lessons from these incidents is more important than ever. The Verizon Data Breach Investigation Report (DBIR), compiled by a team of expert analysts...
In today’s episode, we cover two important data models and their applicability to security. I am talking about data lake and data warehouse. I will look into their similarity, differences and practical considerations surrounding these two...
This is episode 2 of on how how exactly cybercriminals join forces for profit. Make sure you caught up with episode 1 first before you listen to this episode.Lets continue demystifying their collaborative nature.But before that, we will recap...
It is true, there is no loyalty between criminals but there is a profit to be made between them.How exactly cybercriminals join forces for profit? We will answer that question in this week’s episode as we uncover the secret collaborations of...
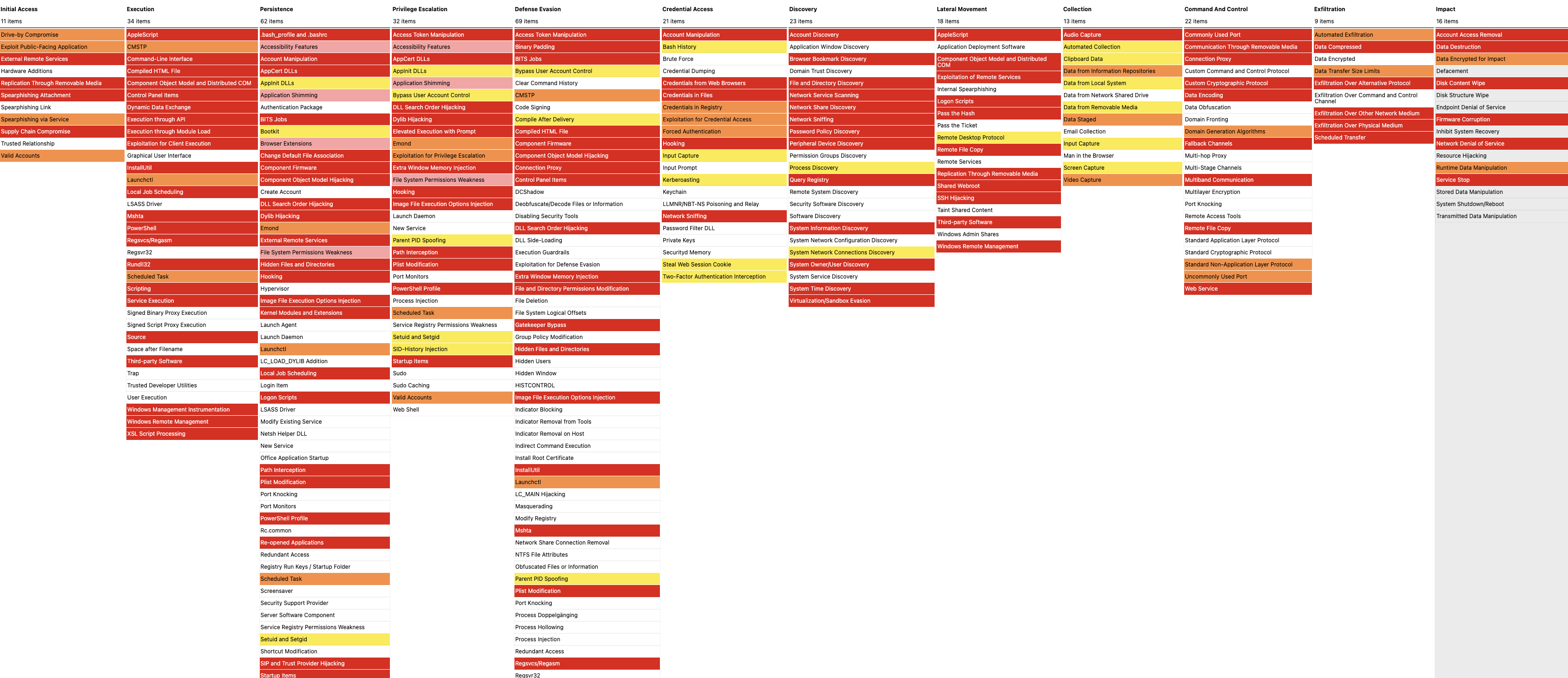
The ATT&CK Navigator is a web-based tool created and maintained by the Mitre organisation. The tools is used for annotating and exploring ATT&CK matrices. It is often used to visualize defensive coverage, red/blue team planning, the...