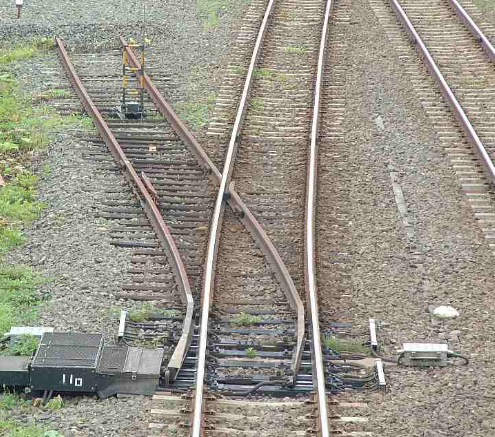
For modern processing to optimise their data crunching, they do something called branch prediction. For example in a high level, if you have an IF statement and if x=1 you would do one thing and if x=0 would do another. What modern processors might do is execute both instructions until it figures out which one of those two instructions was the correct path that should have taken. This is essentially to save time. So it executes the two instructions in parallel and immediately when it figures out what the value of x is it goes ahead and takes the right result.The processor is then suppose to throw away the left over result, the result taken on the other branch which is now no longer needed. Even though the processor would do that correctly and would erase the data computed on the branch that was not taken there will be a residue in memory based on the non taken branch. That residue in memory could involve cryptographic keys or other sensitive material. This is the flaw of branch prediction approach. So with hindsight we now know that the processor gives preference to speed over security.
The researchers were able to show that they could get access to that left over data through a complicated mechanism. So a data computed on a branch that was never actually taken were still accessible. That is the crux of the branch prediction flaw which gave us the vulnerability which we now know as Spectre