The white is pushing companies to adopt defensive measure after an unrepresented rise in ransomware attacks so far this year and in April and May in particular.
“The bluntly worded open letter followed a string of escalating ransomware attacks that stopped gasoline and jet fuel from flowing up the East Coast and closed off beef and pork production from one of the country’s leading food suppliers.” wrote the New York Times.
There are many issue to be dealt with but let me boil down the problem with ransomware into two main issues; lack of preparedness due to lack of experience by personnel or mis-prioritisation of risks because a ransomware attack looks too distant -I am referring to the mantra such “Oh we are too unimportant for anyone to attack us.” The reality is that everyone is a target for the cybercrooks.
Separation of duties
More recently ransomware gangs adopted a high return of investment tactis. They aim at where it hurts most. Take the example of Colonial pipeline where they encrypted the billing systems and not the IT or supply chain infrastructure. They know hitting this part of the company will quick bring the entire organization to its knees because they will not bill their customer. That is exactly what happened and ultimately Colonial Pipeline had to shut supply as they were unable to invoice the clients.
It is therefore important to segment critical part of the network and assign access to those who have legitimate right to interact that part of the infrastructure. By doing so you will stop the fire propagated to the whole of the organization.
Segmentation
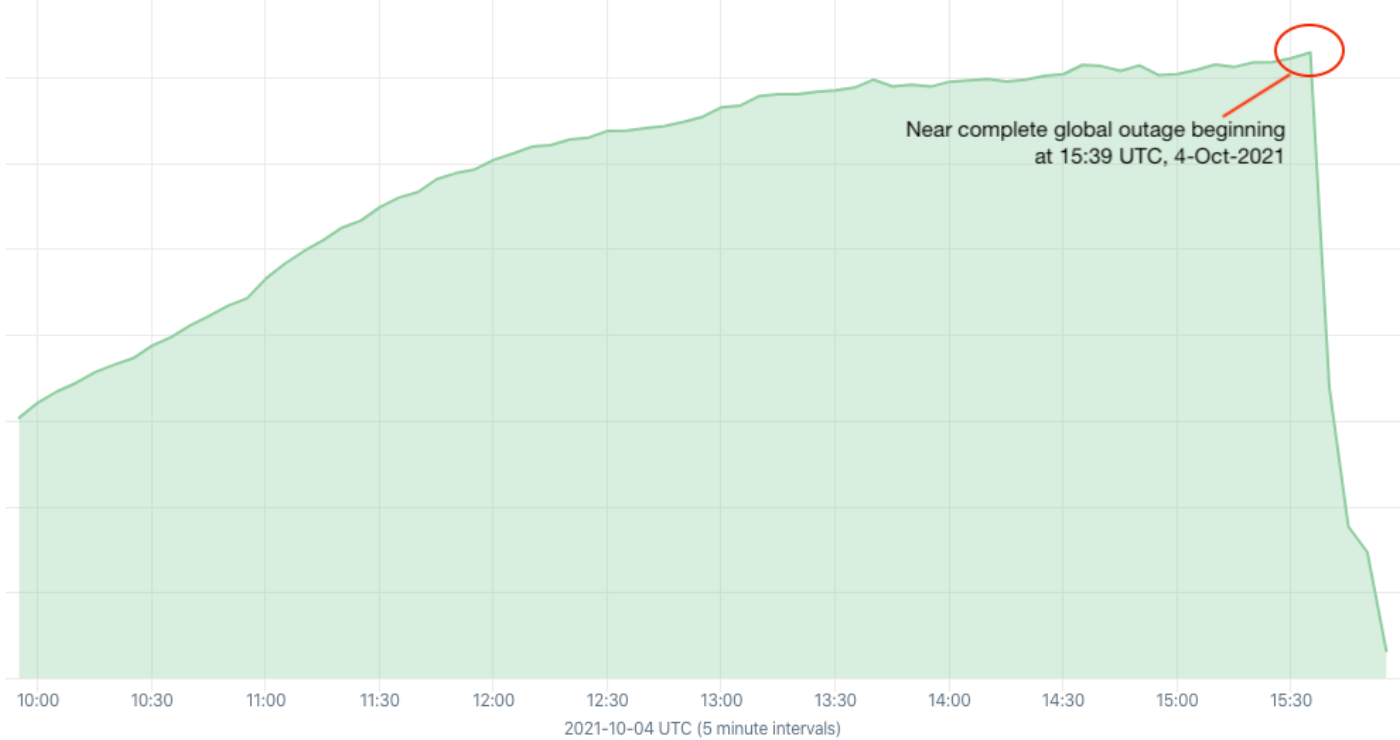
Separating different part of your network by a clear network topology is also parament. Ransomware has been made worm-able and impact organization assets as much as they can possibly get away with it. The idea cyber criminals have adopted is simple. If they can impact far and wide, IT personnel will face an insurmountable challenge. It is impossible to re-built a large of number of machines in a short time despite having functioning backups. The business cannot wait.
So a lot of business opt to pay the cyber crooks and although this might might help the victim somewhat, it also helps the attacker reinvest their ill gotten ransom to attack more victims.
Given that ransomware can penetrate organizations in multiple ways, reducing the risk of ransomware infections requires a portfolio-based approach, rather than a single product. The good news is that most of organization have tools but they are not aligned well to work well tougher. They are siloed.
The industry is starting to take the impact of ransomware more seriously by putting up coordinated efforts -including law enforcement, to disrupt the gangs behind ransomware and their affiliates.